Disable VBS in Windows 11 for Real Gaming Performance Gains

Windows 11’s Virtualization-Based Security, often enabled by default, can quietly reduce performance in CPU-bound games by 10 to 15 percent. This guide explains how to check whether VBS is active, how to disable it safely across Settings, Registry and firmware layers, and what you gain or lose by doing so. As Windows increasingly leans on hardware-backed isolation, understanding how VBS interacts with gaming workloads has become essential for players and professionals who want predictable, low-latency performance.
Quick Steps, Disable VBS Immediately
For users who simply want a fast and reliable way to turn off VBS and recover lost FPS, these steps provide the shortest path. They are designed for maximum clarity and snippet-ready presentation.
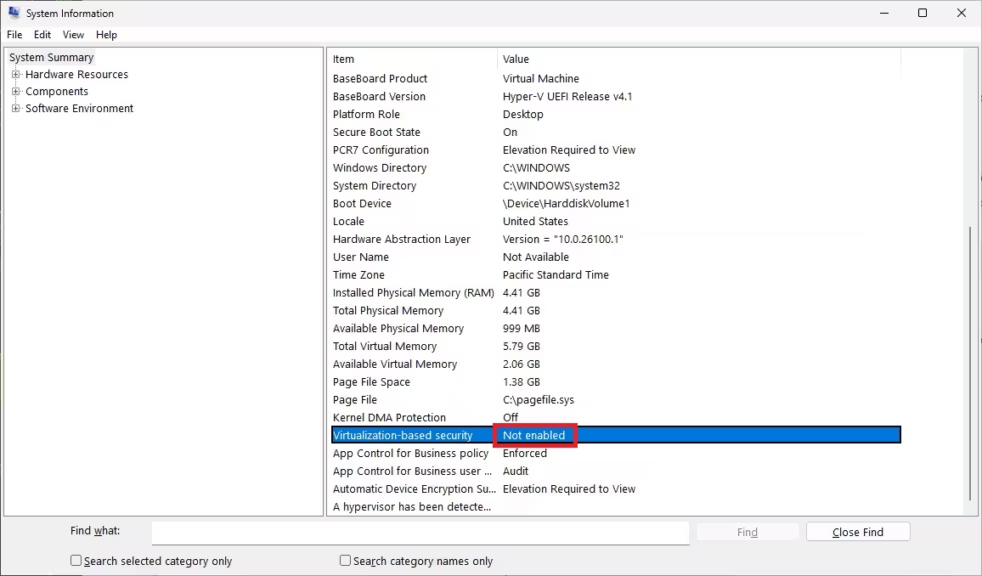
Step 1, Check VBS status with msinfo32
Open the Start menu, type msinfo32, and look for the Virtualization-based Security field. If it says Running or Enabled, VBS is active and the hypervisor is loaded. This diagnostic confirms the system state upfront, avoiding unnecessary changes.
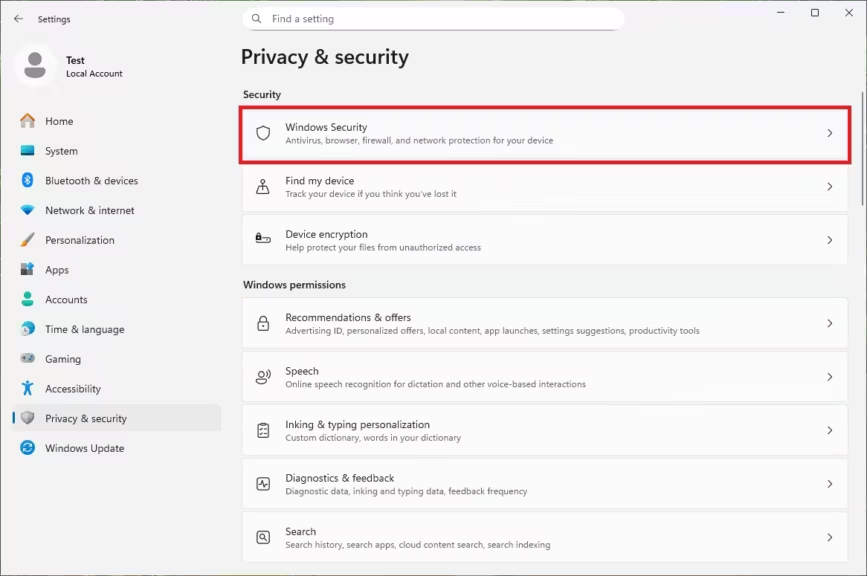
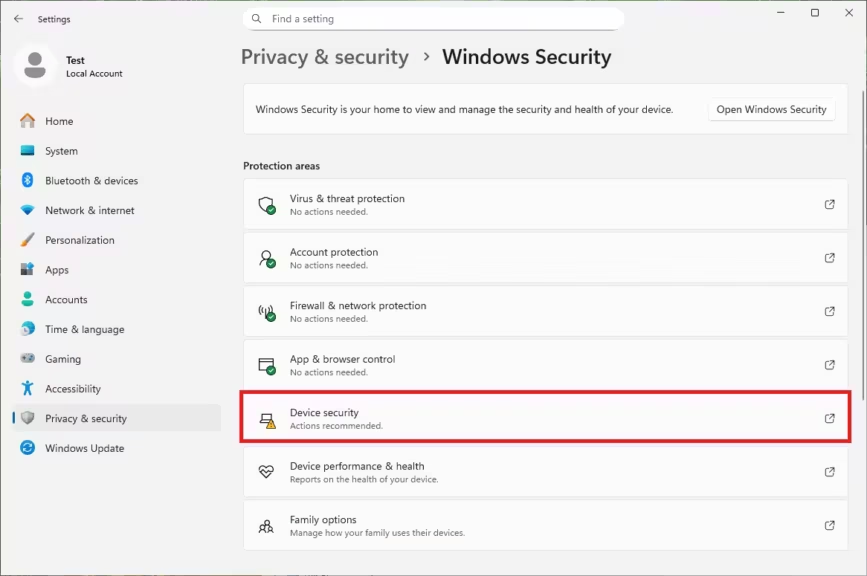
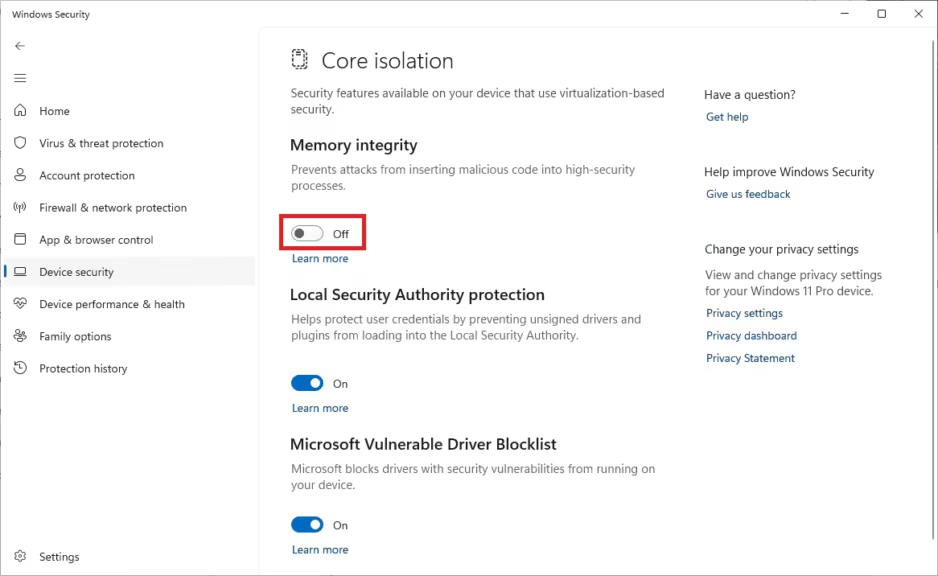
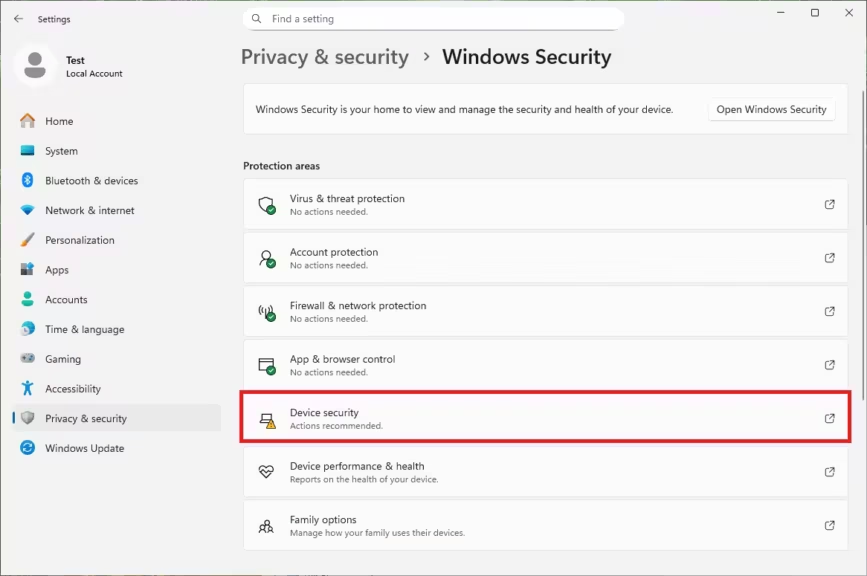
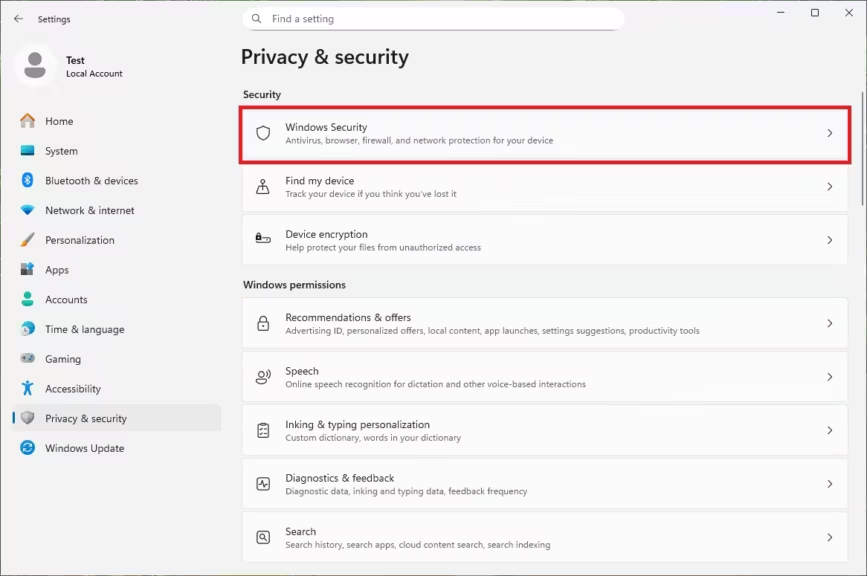
Step 2, Turn off Memory Integrity in Windows Security
Go to Settings, Privacy and Security, Windows Security, then Device Security. Open Core Isolation and disable Memory Integrity. Reboot when prompted. This step turns off HVCI, the component that introduces most of the performance overhead, but it does not always disable VBS entirely.
Step 3, Reboot and reconfirm VBS state
After restarting, open msinfo32 again and recheck VBS status. If it remains active, additional components are still loaded and you will need the more advanced methods below. This verification step ensures you do not assume VBS is off when it is only partially disabled.
What VBS Actually Is and Why It Affects Gaming
Virtualization-Based Security is often described as a simple toggle, but in practice it is an architectural layer built on virtual secure mode and a hardware hypervisor. Windows uses these mechanisms to isolate sensitive processes, enforce kernel integrity and protect credential material. These protections come with measurable overhead in scenarios where CPU latency and thread scheduling are critical, including a large share of modern PC games.
Virtual Secure Mode, Hypervisor, and Hardware Isolation
VBS relies on Intel VT-x or AMD SVM to create a protected environment isolated from the main Windows kernel. Services such as Credential Guard and HVCI run inside this virtual secure mode, with the Hyper-V hypervisor mediating access to memory and kernel operations. Because these hooks sit on the critical path of system calls, they influence any workload that frequently interacts with the kernel.
Why VBS Adds CPU Overhead
Games with complex simulation loops or high draw-call frequency hit kernel boundaries far more often than simple workloads. When HVCI is active, each of these transitions requires validation by VBS mechanisms, increasing CPU time and adding latency. In CPU-limited titles, where the main thread is already strained, this overhead translates directly into lower FPS.
Effects on CPU-bound vs GPU-bound Workloads
In CPU-bound games and at lower resolutions where the GPU is not the bottleneck, VBS overhead is fully visible and can amount to double-digit performance losses. At higher resolutions, GPU-bound workloads mask much of the impact because frame rendering dominates execution time. Recognizing this distinction helps users form accurate expectations about potential performance gains.
Performance Impact, Real-World Benchmarks
Not all games react the same way when VBS is enabled. The performance cost depends heavily on how the engine interacts with the CPU. Games built around dense simulation, complex world updates or high-frequency draw calls show the most visible impact. GPU-bound titles, especially at 1440p or 4K, see far fewer changes.
Gains in CPU-bound Games
Simulation-heavy games like Microsoft Flight Simulator or large open-world engines rely on a main thread that interacts extensively with the kernel. With VBS active, these interactions route through the hypervisor, adding extra latency and validation. Disabling VBS typically restores 10 to 15 percent of performance in these titles, improving both raw FPS and frame-time consistency.
Gains in AAA and e-sport titles
AAA titles that mix CPU and GPU workloads—Cyberpunk 2077, Far Cry 6, Starfield—show moderate benefits in the 4 to 6 percent range when VBS is off. Competitive games like Valorant or CS2 are more optimized, but disabling VBS still produces small yet measurable gains of 2 to 4 percent, important for players seeking 240 Hz or higher refresh-rate stability. These improvements are modest but non-trivial in high-refresh environments.
Impact variations by CPU generation
Older or lower-core-count CPUs suffer most from VBS overhead because virtualization hooks consume a larger share of their available execution budget. Newer AMD and Intel CPUs handle VBS more efficiently, but the impact does not disappear completely. Understanding where your hardware bottlenecks appear helps predict whether disabling VBS will deliver noticeable gains.
Semi-quantitative performance impact by CPU generation (VBS On vs Off)
| CPU Generation / Architecture | Typical VBS Overhead | Expected Gain When Disabled | Notes |
|---|---|---|---|
| Intel 6th–8th Gen (Skylake → Coffee Lake) | High (10–15%) | +10–15% | Older virtualization pipeline, weaker single-thread performance. |
| Intel 9th–10th Gen (Coffee Lake R → Comet Lake) | Medium-High (7–12%) | +8–12% | Improved IPC but still sensitive to hypervisor transitions. |
| Intel 11th–12th Gen (Rocket Lake → Alder Lake) | Medium (5–9%) | +6–10% | Hybrid architecture mitigates some overhead, still noticeable. |
| Intel 13th–14th Gen (Raptor Lake → Refresh) | Low-Medium (3–6%) | +4–7% | Strong single-thread performance, overhead smaller but present in CPU-bound titles. |
| AMD Zen 1 / Zen+ (Ryzen 1000 / 2000) | High (9–14%) | +10–14% | Early Zen architectures highly sensitive to virtualization layers. |
| AMD Zen 2 (Ryzen 3000) | Medium-High (7–12%) | +8–12% | Better, but still non-trivial overhead in simulation-heavy games. |
| AMD Zen 3 (Ryzen 5000) | Medium (5–8%) | +6–9% | Much improved latency handling reduces VBS penalty. |
| AMD Zen 4 / Zen 5 (Ryzen 7000 / 9000) | Low-Medium (3–6%) | +4–7% | Excellent single-thread performance, most overhead masked at higher resolutions. |
Key takeaways
- Older CPUs lose the most when VBS is enabled because virtualization overhead consumes a larger share of available single-thread performance.
- Modern CPUs mask part of the VBS cost, but CPU-bound engines still show meaningful improvement when VBS is disabled.
- Simulation-heavy and competitive titles benefit the most across all generations.
Method 1, Disable VBS Through Windows Settings
Windows Settings is the most accessible entry point for turning off VBS, especially for mainstream users. However, because VBS is composed of multiple subsystems, this approach often disables only a portion of its functionality.
Toggling Memory Integrity and Core Isolation
Navigate to Settings, Privacy and Security, Windows Security, then Device Security. Under Core Isolation, switch Memory Integrity off and restart your PC. This disables HVCI, the component responsible for most of VBS’s performance tax, but it does not shut down the underlying virtual secure mode.
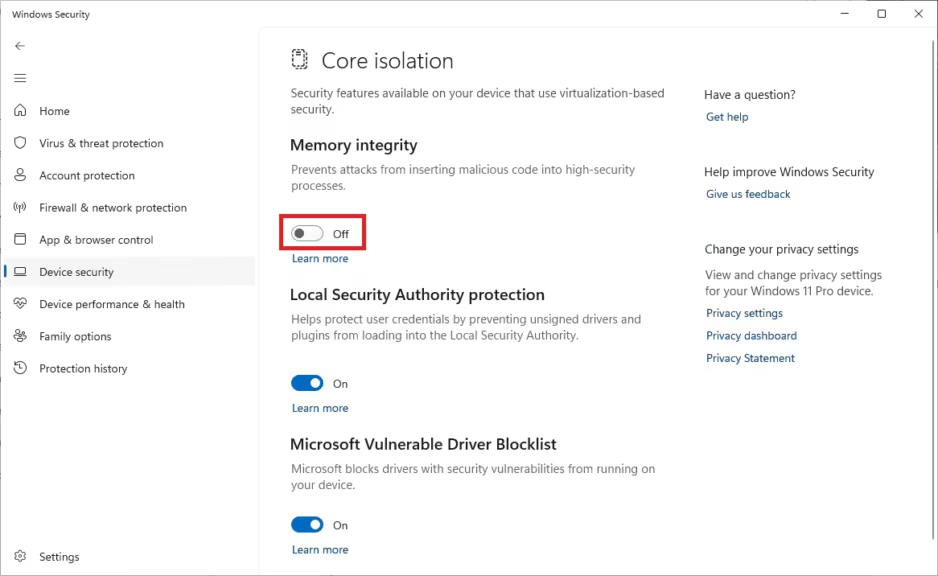
Understanding incomplete disable states
A significant number of users report that VBS remains active even after Memory Integrity has been switched off. This happens because VBS is made of several layers: Secure Launch, Credential Guard, hypervisor initialization and more. If any of these remain enabled, VBS continues to load at boot, producing the same performance impact.
Verifying changes and common pitfalls
After making any change, reboot and check VBS status in msinfo32. If VBS is still listed as Running, the system is still initializing at least one subsystem tied to VBS. Resolving this requires the more advanced steps in the next section.
Method 2, Disable VBS via Registry or Group Policy
For advanced users, developers or IT professionals, the Registry and Group Policy provide deterministic control over the VBS stack. Unlike the graphical interface, which often disables only surface-level components, these methods allow you to prevent Virtual Secure Mode from loading at all, ensuring predictable, reproducible performance behavior.
Critical DeviceGuard keys (EnableVirtualizationBasedSecurity, RequirePlatformSecurityFeatures)
Open regedit and navigate to:
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlDeviceGuardTwo keys determine whether the system initializes VBS at boot:
- EnableVirtualizationBasedSecurity
- RequirePlatformSecurityFeatures
If they are missing, create them manually:
- Right-click DeviceGuard, choose New, then DWORD (32-bit).
- Name the first key EnableVirtualizationBasedSecurity and set its value to 0.
- Create the second key RequirePlatformSecurityFeatures and set it to 0 as well.
Setting these values to zero tells Windows not to start Virtual Secure Mode and prevents the hypervisor from entering its secure enforcement path. These edits carry system-wide implications, so advanced users should create a restore point or full backup before modifying these keys.
Group Policy controls for enterprise or Pro users
On Windows 11 Pro, Enterprise or Education SKUs, Group Policy provides deeper configuration granularity suitable for managed systems or technical environments.
Open gpedit.msc and navigate to:
Computer Configuration > Administrative Templates > System > Device GuardFrom here, administrators can configure:
- virtualization-based security requirements,
- Credential Guard policies,
- Secure Launch behavior,
- hypervisor-enforced code integrity settings.
Group Policy-based configuration is more stable across reboots and Windows updates, making it the preferred approach for fleet management or long-term configurations.
Windows Hello, BitLocker, and reinforcements
Some Windows security features implicitly rely on VBS. Windows Hello (especially PIN-based login), BitLocker with TPM-backed keys, and Secure Boot can reactivate VBS dependencies or override user-set Registry values. If VBS reappears after a reboot, temporarily disabling Windows Hello or reviewing BitLocker device encryption settings may be necessary to fully shut down VBS.
Method 3, Disable Virtualization at Firmware Level (Intel VT-x / AMD SVM)
Disabling virtualization in the BIOS or UEFI is the most definitive way to prevent Virtual Secure Mode from initializing. This approach blocks the hypervisor at the hardware level and guarantees that VBS cannot load, regardless of Windows settings or Registry keys.
VT-x/SVM interactions with VBS and Hyper-V
VBS requires hardware-backed virtualization, either Intel VT-x or AMD SVM, to construct isolated memory regions and enforce kernel integrity. If these features are disabled in firmware, Windows cannot load the Hyper-V hypervisor, which in turn prevents VBS from starting. This ensures complete deactivation, even on systems where OEM presets or Windows updates repeatedly re-enable VBS.
Breaking points, WSL2, VMs, emulators
Disabling VT-x or SVM has major consequences for development and simulation environments. Turning off hardware virtualization disables:
- Hyper-V,
- WSL2 (which relies entirely on virtualization),
- Android emulators that use hardware acceleration,
- VMware and VirtualBox fast virtualization paths,
- Windows Sandbox and container-based workflows.
For software engineers, penetration testers, cloud developers or researchers, this trade-off is substantial. Before disabling virtualization, consider whether your workload depends on VM acceleration or kernel-isolated environments.
OEM inconsistencies and UEFI quirks
Firmware menus differ dramatically across motherboards and laptops. Virtualization settings may be buried under CPU Configuration, Security, Advanced Settings or vendor-specific submenus. Some OEMs also lock these features behind administrative passwords or enforce specific security presets that auto-enable virtualization after firmware updates.
Troubleshooting, When VBS Refuses to Disable
Even after disabling Memory Integrity or editing DeviceGuard keys, some systems continue loading VBS during boot. This persistence is not a bug but a byproduct of Windows 11’s layered security model, OEM presets and update logic. Understanding these interactions helps diagnose why VBS remains active despite user changes.
Windows 11 24H2 re-enabling components
Major feature updates, including Windows 11 24H2, may silently restore VBS requirements by resetting DeviceGuard baselines or toggling Secure Launch back on. These updates can also reapply OEM security templates that require the hypervisor. After each cumulative or feature update, verify VBS status via msinfo32 and reapply the necessary Registry or Group Policy configuration.
OEM presets and hidden virtualization toggles
Some prebuilt systems and laptops ship with OEM security profiles designed to pass enterprise compliance tests. These may silently enforce virtualization at the firmware level or re-enable related flags during boot. If VBS persists after Registry and Settings modifications, review UEFI menus and disable any vendor presets tied to “security enhancements”, “secure virtualization”, or “trusted launch”.
Mixed states, Memory Integrity off but VBS still enabled
One of the most common user reports is that Memory Integrity is disabled, yet msinfo32 still shows VBS as Running. This happens because VBS consists of multiple components: Secure Launch, Credential Guard, HVCI, hypervisor initialization and more. Even if HVCI is off, the hypervisor may still load, leaving VBS partially active and maintaining the performance overhead. Resolving mixed states requires Registry-level or firmware-level changes.
Security Trade-offs, What You Lose by Disabling VBS
Disabling VBS increases gaming performance by removing virtualization overhead, but it also reduces the system’s defensive architecture. Understanding what protections are lost is essential for users balancing performance with security posture.
Loss of kernel-mode protections
Virtual Secure Mode enforces kernel code integrity and prevents unauthorized drivers or tampered components from loading. With VBS disabled, the kernel becomes more exposed to sophisticated rootkits and memory manipulation attacks that target low-level components. While rare in consumer environments, these threats matter for users connecting to untrusted peripherals or experimenting with drivers.
Credential Guard, LSASS isolation, risk profiles
Credential Guard isolates authentication artifacts such as NTLM hashes and Kerberos tickets. Turning off VBS disables this isolation, increasing the risk of credential theft if malware reaches the system. The risk profile differs across users: low for gaming-only rigs, moderate for mixed-use desktops, and high for enterprise-connected devices.
Home gaming rigs vs mixed-use machines
For pure gaming systems, disabling VBS usually offers a straightforward benefit. For dual-purpose PCs used for work, remote access or enterprise tasks, the decision requires a more cautious evaluation. Users must weigh predictable high FPS against reduced kernel hardening.
Benchmarks Summary Table and Quick Reference
VBS impacts gaming performance unevenly, depending on how the engine uses CPU resources. Below is a simplified summary of typical performance differences with VBS On and Off.
VBS On vs Off comparison table
| Game / Workload | VBS On Impact | VBS Off Gain | Notes |
|---|---|---|---|
| Microsoft Flight Simulator | Heavy | +10–15% | Strongly CPU-bound |
| Cyberpunk 2077 | Moderate | +4–6% | Mixed CPU-GPU load |
| Far Cry 6 | Moderate | +4–6% | Benefits from faster thread scheduling |
| Valorant, CS2, Fortnite | Light | +2–4% | High refresh-rate titles |
| 4K GPU-bound workloads | Minimal | ~0–2% | GPU-limited scenarios |
CPU and resolution sensitivity notes
Performance gains scale with CPU bottlenecks. At 1080p or in simulation-heavy titles, the overhead introduced by VBS is fully exposed. At higher resolutions, rendering dominates execution time, masking security-induced latency. Understanding this relationship helps users determine whether disabling VBS will deliver meaningful improvements.
Advanced Considerations for Professionals
For developers, system integrators, cybersecurity analysts and researchers, controlling VBS is not just a performance tweak but an operational requirement. The ability to explicitly manage the hypervisor stack matters in workflows involving virtualization, debugging or low-level system engineering.
Scriptable VBS state management
Power users can script VBS and hypervisor checks through PowerShell or deployment tooling. Exporting Registry templates and reapplying them after Windows updates ensures consistent behavior across reboots. In lab environments, automated auditing helps detect when updates unexpectedly re-enable virtualization.
Infrastructure and fleet considerations
In enterprise or research environments, disabling VBS is a governance decision. IT teams must consider compliance requirements, threat models and hardware capabilities before altering VBS baselines. Group Policy, MDM solutions and configuration baselines remain the preferred tools for managing VBS in large fleets.
Anti-cheat compatibility on competitive titles
Some anti-cheat systems interact with virtualization features for tamper detection. While most modern engines operate without VBS, rare edge cases exist where anti-cheat systems may require or expect certain virtualization states. Professionals in QA or esports operations should verify compatibility when making configuration changes.
Overall Takeaway
VBS strengthens Windows 11 with meaningful kernel and credential protections, but these safeguards introduce measurable overhead in CPU-bound gaming workloads. For players, enthusiasts and professionals who need predictable low-latency performance, disabling VBS can restore 10 to 15 percent of lost FPS, especially in simulation-heavy or main-thread-limited titles. The real value lies in choosing the right control layer, Settings, Registry or firmware, based on how your system is used and how much security you are willing to trade for performance. As Microsoft continues to expand hardware-backed protections across its platform, targeted tuning of virtualization layers will remain an important skill for anyone who expects deterministic performance from Windows 11.
Sources et références
1. Tech media
- 2025, As reported by XDA Developers, Windows 11 security and VBS explanations, https://www.xda-developers.com/microsoft-makes-windows-11-24h2-more-secure/
- 2025, As covered by Hone.gg, recommended optimization practices for gaming systems, https://support.hone.gg/hc/en-gb/articles/4758238924959-Recommended-Optimizations-to-Use
- 2024, As reported by Jaspreet.net, detailed VBS disabling methods and analysis, https://www.jaspreet.net/2024/10/11/2731/how-to-properly-disable-virtualization-based-security-vbs-in-windows-11-24h2/
- 2024, As explained by Beebom, Windows configuration and policy insights, https://beebom.com/how-enable-group-policy-editor-windows-11-home/
- 2023, According to Tom’s Hardware, benchmark results on VBS performance impact, https://www.tomshardware.com/news/windows-vbs-harms-performance-rtx-4090
- 2023, As noted by Hardware Times, measured slowdowns in CPU-bound workloads, https://hardwaretimes.com/this-windows-11-setting-makes-your-pc-up-to-11-slower-in-gaming/
2. Companies
- 2025, Asus, MSI and OEM security presets referenced in firmware documentation (general homepages only).
- 2024–2025, Various OEM vendors reinforcing virtualization defaults after Windows updates.
3. Institutions
- 2025, As referenced by security publications, guidance on virtualization and credential isolation (general homepages only).
4. Official sources
- 2025, As stated in Microsoft’s documentation, VBS architecture and device security features, https://learn.microsoft.com/en-us/windows-hardware/design/device-experiences/oem-vbs
- 2025, According to Riot Games documentation on Vanguard security interactions, https://support-valorant.riotgames.com/hc/fr/articles/360046160933-Qu-est-ce-que-Riot-Vanguard
- 2025, As listed in Riot Games Restrictions Vanguard guidelines, https://support-valorant.riotgames.com/hc/fr/articles/22291331362067-Restrictions-Vanguard
- 2025, As detailed by JumpCloud, VBS security architecture and associated risks, https://jumpcloud.com/it-index/what-is-virtualization-based-security-vbs
- 2025, As described by NinjaOne, virtualization-based enforcement and verification methods, https://www.ninjaone.com/blog/core-isolation-virtualization-based-security/
- 2024, As outlined by Azalio.io, Microsoft’s open-source paravisor architecture, https://www.azalio.io/openhcl-understanding-microsofts-open-source-paravisor/
- 2025, As referenced by WiseCleaner, registry and system configuration guidance, https://www.wisecleaner.com/how-to/352-how-to-automatically-and-securely-clean-the-registry.html
- 2025, As sourced from Reddit user reports and troubleshooting patterns, https://www.reddit.com/
- 2025, According to The Software Guy on YouTube, practical benchmarks and VBS testing, https://www.youtube.com/watch?v=hKM_FOXJS0k
Your comments enrich our articles, so don’t hesitate to share your thoughts! Sharing on social media helps us a lot. Thank you for your support!