Running a PowerShell script via Windows 11 Task Scheduler
Automating PowerShell (.ps1) scripts within a professional Windows environment requires a rigorous configuration to ensure operational reliability. For a comprehensive overview of automation solutions, it is essential to understand the underlying mechanisms of the Windows Task Scheduler. By default, Windows does not treat .ps1 files as executables but as text files for security reasons, often opening them in Notepad or an IDE.
To ensure a task runs without interruption, you must explicitly call the PowerShell host and configure the execution environment to be hermetic and self-contained.
Action configuration: the robust method
A common mistake is entering the script’s path directly into the “Program/script” field. This method is unstable and relies on inconsistent shell associations. Standard systems administration practice dictates calling the full path of the executable to avoid issues with the PATH environment variable, which can vary depending on the task’s security context.
- Program/script: Enter the absolute path to the PowerShell host:
- PowerShell 5.1 (Standard):
C:WindowsSystem32WindowsPowerShellv1.0powershell.exe - PowerShell 7 (Core):
C:Program FilesPowerShell7pwsh.exe
- Add arguments (optional): Use a structured argument string (see the production section below).
- Start in (optional): Enter the parent directory of your script. This is a critical step: without it, the default working directory will be C:WindowsSystem32, which will cause any script using relative paths or local log writing to fail.
Recommended production arguments
For a production-ready scheduled task, the call must be non-interactive and isolated from user profiles that might load slow modules or generate unexpected errors.
Recommended syntax: -NoProfile -NonInteractive -NoLogo -ExecutionPolicy Bypass -File "C:ScriptsMyScript.ps1"
Parameter breakdown
- -NoProfile: Prevents the loading of the user’s PowerShell profile ($PROFILE). This speeds up startup and prevents conflicts with custom alias or function scripts.
- -NonInteractive: Ensures the script does not present an interactive prompt, which would hang a background task indefinitely.
- -NoLogo: Hides the copyright banner at startup, keeping output logs clean.
- -ExecutionPolicy Bypass: Temporarily ignores execution restrictions for this specific process. This is the cleanest way to run a script without globally lowering system security. For deeper insights, refer to the official Microsoft Learn – Execution Policies documentation.
Security and script integrity
Using the Bypass flag is a convenience mechanism, not a security vulnerability in itself. The real risk lies in the integrity of the .ps1 file.
- Access Control (ACL): Scripts should be stored in directories where only Administrators or a specific Service Account have “Write” permissions.
- Digital Signing: In high-security environments, prefer the AllSigned policy. This requires every script to be signed by a trusted certificate before execution.
- Execution Context: In the General tab, the option “Run whether user is logged on or not” switches the task to a non-interactive session (Session 0).
- Mapped network drives (e.g., Z:*) will not be available. You must use UNC paths (ServerShare*).
- User-specific environment variables will not be loaded.
Common Task Scheduler errors
If your task fails to produce the expected result, check the following return codes and behaviors:
- Error Code 0x1: Usually indicates a PowerShell syntax error or a file path not found. Test your command line manually in a terminal first.
- Status 0x41301 (Running): The task is considered still active. This often happens when a command waits for user input (highlighting the need for -NonInteractive).
- Unmanaged Relative Paths: If your script fails to find source files, verify the “Start in” field.
- Insufficient Permissions: For system-level operations, check “Run with highest privileges”. This is typically required when automating Windows 11 backup and WSL environments.
For complex debugging, the community on StackOverflow provides extensive documentation on security context edge cases.
Quick guide: “ready-to-paste” block
| Parameter | Recommended Value |
|---|---|
| Program/script | C:WindowsSystem32WindowsPowerShellv1.0powershell.exe |
| Arguments | -NoProfile -NonInteractive -ExecutionPolicy Bypass -File "C:PathToScript.ps1" |
| Start in | C:PathTo |
| Security | Check “Run with highest privileges” |
Once your automation is stable, you can leverage PowerShell to manage more advanced workloads, such as installing vLLM with Docker Compose or orchestrating AI environments. For official structural references, see the Microsoft Task Scheduler Overview.
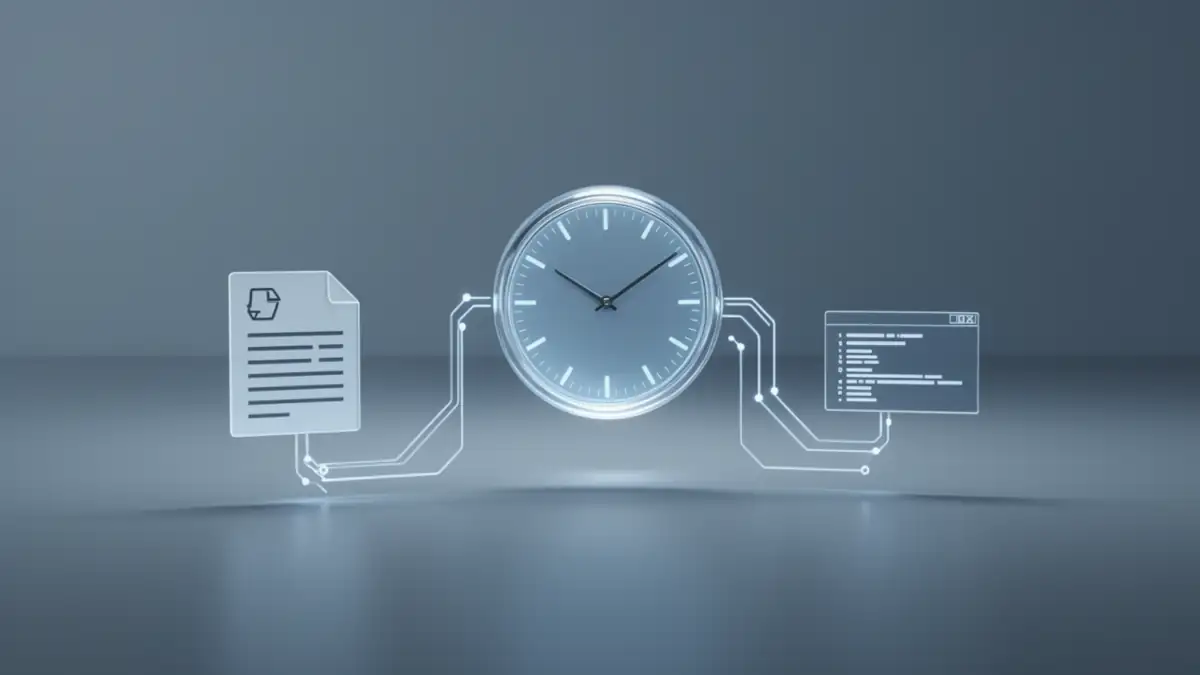
Scheduling a PowerShell script is not enough if your PC is asleep at the scheduled time. For a task to truly run on time, Windows 11 must be allowed to wake from sleep through properly configured wake timers and power settings.
We break down these mechanisms in our dedicated guide on automatic wake scheduling in Windows 11, ensuring your scripts execute reliably even without user interaction.
Your comments enrich our articles, so don’t hesitate to share your thoughts! Sharing on social media helps us a lot. Thank you for your support!