Securing WSL mirrored networking: a technical deep dive into architecture and exposure
The release of networkingMode=mirrored for the Windows Subsystem for Linux (WSL), introduced with WSL 2.0.0 in the September 2023 update, represents a significant architectural shift from the traditional NAT-based virtualization. While NAT provided a layer of implicit isolation, mirrored mode integrates Linux network namespaces directly into the host’s stack. For developers managing machine learning workflows on WSL or complex agentic workflows on Windows 11, understanding the security implications of this transition is paramount.
Architecture: moving beyond NAT
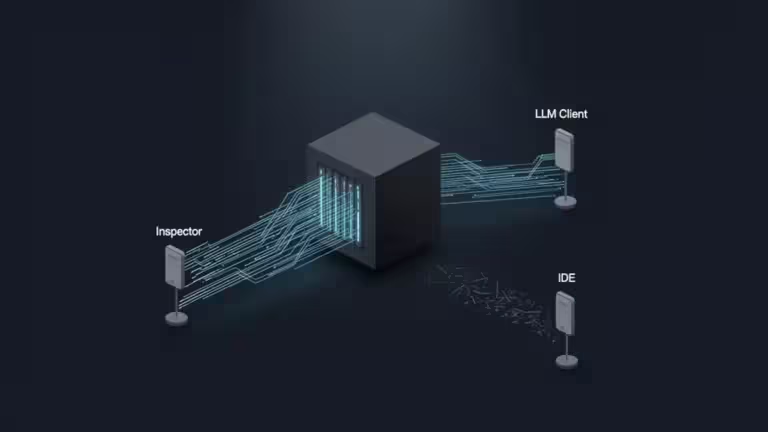
In the legacy NAT mode, WSL operates within a virtualized network, hidden behind a virtual switch that handles address translation. In contrast, networkingMode=mirrored utilizes Hyper-V networking integration mechanisms to allow the Linux environment to behave as a peer to the Windows host on the network.
Rather than simple interface cloning, mirrored networking synchronizes the network state between Windows and the Linux VM. This enables WSL to handle complex networking tasks—such as IPv6 traffic, VPN compatibility, and Multicast—with the same fidelity as a physical host.
Prerequisites and initialization
Before deploying mirrored networking, ensure your environment meets the minimum requirements:
- OS: Windows 11, version 22H2 or later.
- WSL: Latest version (check with wsl –version).
To verify your current state, execute:
wsl --statusTechnical comparison: NAT vs. Mirrored mode
The choice between these modes dictates the boundary of your security perimeter.
| Feature | NAT Mode | Mirrored Mode |
|---|---|---|
| IP Address | Virtual (typically 172.x.x.x) | Host LAN IP |
| Isolation | High (via NAT boundary) | Low (Direct LAN presence) |
| IPv6 Support | Limited / NAT64 | Full Native Support |
| LAN Exposure | Manual (Port Forwarding) | Native (Interface Binding) |
| Firewall Integration | Indirect (Host-based) | Direct (Host-integration) |
Service exposure and the 0.0.0.0 fallacy
A common misconception is that mirrored mode indiscriminately exposes all WSL services to the local network. In reality, exposure is governed by the service’s binding configuration.
- Secure Binding: Services bound to 127.0.0.1 or ::1 remain strictly local to the machine.
- Network Exposure: Services bound to 0.0.0.0 (IPv4) or :: (IPv6), or specifically to the host’s LAN IP, become accessible to other devices on the network.
In a mirrored configuration, a database or web server listening on 0.0.0.0 is effectively “naked” on your LAN. This is particularly critical regarding IPv6; depending on your network configuration, mirrored networking may assign globally routable IPv6 addresses to the WSL instance. Without properly configured Windows Defender Firewall rules, these services could be reachable from the public internet.
Hardening the mirrored environment
To maintain security while leveraging the performance of mirrored networking, a structured hardening approach is required via the %USERPROFILE%.wslconfig file.
Firewall integration
Recent versions of WSL enable firewall integration by default. However, for protecting WSL environments, explicitly verifying the firewall=true setting is a best practice. This ensures that the Windows Filtering Platform (WFP) can inspect and filter traffic entering the Linux namespace.
DNS and Tunneling
The dnsTunneling=true directive improves DNS consistency and ensures that WSL adheres to the same DNS policies as the host, which is essential for compatibility with enterprise VPNs and specialized network topologies.
Recommended .wslconfig
[wsl2]
networkingMode=mirrored
firewall=true
dnsTunneling=trueImportant: Changes to .wslconfig are not hot-reloaded. You must restart the subsystem for settings to take effect:
wsl --shutdownCross-platform diagnostics
An expert-level audit requires verifying the stack from both the Windows host and the Linux guest.
Linux: The Process-Level View (Guest)
Use the ss command to identify which services are listening on external interfaces. According to the Linux ss command documentation, this provides the most accurate view of the socket state.
ss -tulpenLook for : or 0.0.0.0: which indicates LAN-wide exposure.*
How to read the output:
127.0.0.1:[port]: The service is bound to the loopback interface. It is secure and not reachable by other devices on the LAN.
0.0.0.0:[port] or *:[port]: The service is “listening on everything.” In mirrored mode, this makes the service publicly available to your local network.
Windows: The Global Exposure View (Host)
The PowerShell script below identifies which ports are open across the entire machine. Since WSL shares the host’s IP in mirrored mode, any service listening on 0.0.0.0 or :: in Linux will appear here as a globally exposed port on the Windows host.
Run this PowerShell script as Administrator to see how the host perceives the mirrored ports:
Get-NetTCPConnection -State Listen |
Select-Object LocalAddress, LocalPort, @{Name="Exposure"; Expression={
if ($_.LocalAddress -in "0.0.0.0", "::") {"LAN EXPOSED"} else {"LOCAL"}
}} | Sort-Object LocalPortWhy this matters: This provides a “hacker’s view” of your machine. If you see a port like 8080 or 5432 marked as LAN EXPOSED, it means any device on your internal network can reach that service.
If PowerShell shows a port is exposed, use the ss command in Linux to find the PID (Process ID). You can then run ps -p [PID] -o comm= to identify the exact application that needs to be reconfigured to bind to 127.0.0.1.
Realistic risk assessment: lateral movement and exposure
Moving from NAT to mirrored mode effectively removes the “network airlock” between your Linux development environment and the rest of your local network. While the risks are manageable, they shift from virtualization-related issues to standard networking vulnerabilities.
- Network Scanning and Discovery: Since WSL shares the host’s LAN identity, it becomes a visible node for network scanners. An attacker who has gained a foothold on another device in your internal network (such as a compromised IoT device) can directly probe your WSL services for weak authentication or unpatched vulnerabilities.
- Lateral Movement: In the event of a Linux-side compromise—perhaps via a malicious NPM package or a vulnerable Docker image—the attacker is already “inside” your LAN. They can use the mirrored interface to scan other internal servers, NAS devices, or workstations without having to break out of a NAT-restricted subnet first.
- Exposed Development Services: Many tools (e.g., Webpack Dev Server, Vite, or Flask) default to unencrypted HTTP. In mirrored mode, if bound to 0.0.0.0, your session tokens and development data are transmitted in cleartext across the local Wi-Fi or Ethernet segment.
When NOT to use mirrored networking
Despite its performance benefits, mirrored mode is not a universal replacement for NAT. Engineers should revert to NAT or exercise extreme caution in the following scenarios:
- Public Wi-Fi Environments: When working from cafes, airports, or conferences, your WSL services are exposed to a hostile local segment. Unless your Windows Firewall is strictly configured to “Public” profile with a default-deny policy, mirrored mode is inherently risky.
- Shared or Untrusted Networks: If you do not control the security of the other devices on the LAN, the lack of isolation becomes a liability.
- Security Testing and Malware Analysis: If you are using WSL to analyze suspicious binaries or perform penetration testing, the NAT boundary provides a vital layer of protection that prevents accidental leakage into your production network.
- Travel Laptops: For devices frequently moving between different network trust levels, the consistent isolation of NAT mode is often preferable for maintaining a stable security posture.
Conclusion: Balancing fidelity and security
The transition to networkingMode=mirrored is a powerful tool for modern developers, specifically for those requiring deep network integration for agentic workflows on Windows 11. However, it shifts the burden of security from the platform to the architect. By leveraging firewall=true, enforcing 127.0.0.1 binding, and maintaining regular WSL environment backups, you can harness the full potential of the mirrored stack without compromising your system’s integrity.
For more information on the underlying networking implementation, consult the official WSL networking documentation.
Your comments enrich our articles, so don’t hesitate to share your thoughts! Sharing on social media helps us a lot. Thank you for your support!